Post-Quantum Cryptography Is Becoming a Regulatory Requirement
CNSA 2.0, NIST FIPS 203/204/205, and emerging certification expectations are reshaping how device makers secure embedded systems, IoT products, and connected hardware.
Why regulation is accelerating
The transition to post-quantum cryptography is no longer just a technical issue — it is becoming a regulatory and compliance requirement.
Governments and standard bodies are defining timelines that already impact procurement, certification, and contractual obligations across critical industries.
At the same time, adversaries are collecting encrypted data today to decrypt it in the future — the “harvest now, decrypt later” threat.
As a result, post-quantum migration is a present-day imperative, not a future consideration.

CNSA 2.0 regulatory countdown
The NSA’s Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) provides the most authoritative roadmap for the transition to post-quantum cryptography. While initially defined for National Security Systems, it is widely recognized as the benchmark that will cascade into commercial and regulated markets.
| Year | Requirement |
|
2025 |
CNSA 2.0 algorithms should be supported and preferred |
| 2030 | PQC required for software/firmware signing and traditional networking |
| 2033 | PQC required for OS, web, cloud, and general systems |
| 2035 | Full transition target for National Security Systems |
These milestones represent more than guidance, they define the compliance trajectory for secure systems worldwide, particularly in regulated industries.
Devices and systems expected to operate beyond 2030 must integrate post-quantum cryptography at the design stage. Delaying migration introduces both compliance risk and long-term security exposure.
NIST post-quantum cryptography standards
In August 2024, NIST finalized the first set of post-quantum cryptographic standards, marking a critical milestone in the transition from research to deployment.
These standards define the algorithms that will replace today’s quantum-vulnerable public-key systems.
FIPS 203 — ML-KEM (Key Encapsulation Mechanism)
The primary standard for quantum-safe key exchange, designed to replace protocols such as RSA and Diffie-Hellman.
FIPS 204 — ML-DSA (Digital Signature Algorithm)
The recommended standard for digital signatures, including firmware signing, secure boot, and certificate authority operations.

FIPS 205 — SLH-DSA (Hash-Based Signatures)
A hash-based signature scheme providing algorithmic diversity and resilience, particularly for high-assurance environments.
Why device makers are uniquely exposed
Organizations developing embedded and connected systems face unique challenges in the transition to post-quantum security.
Unlike software, hardware devices operate for 10 to 20 years, creating a gap between device lifecycles and rapidly evolving cryptographic standards.
This risk is amplified by structural constraints:
- Immutable roots of trust: keys in ROM or OTP cannot be updated after manufacturing
- Secure boot dependency: verification relies on algorithms that may become obsolete
- Firmware signing impact: post-quantum signatures are larger and more resource-intensive
- System constraints: increased memory, bandwidth, and performance requirements
- Legacy exposure: many deployed devices cannot be upgraded
As a result, devices designed today with classical cryptography risk becoming vulnerable and non-compliant within their operational lifetime.

Compliance risks for embedded systems
The transition to post-quantum cryptography introduces not only technical challenges but also significant business and regulatory risks.
Failure to anticipate this transition can lead to:
- Non-compliance with procurement requirements in regulated sectors
- Delays in certification processes (Common Criteria, FIPS 140-3)
- Insecure secure boot chains based on deprecated algorithms
- Exposure to long-term data breaches through harvest-now, decrypt-later attacks
- Costly redesigns of hardware platforms after production
- Contractual and reputational risk with customers and partners
Because cryptography is deeply embedded in system architecture, late-stage remediation is often complex, expensive, or impossible.
Where to start: securing the most critical layers
The transition to post-quantum cryptography does not happen uniformly across systems.
Some components can evolve over time. Others — particularly those anchored in hardware — define the long-term security and compliance of the entire device.
A successful strategy begins by identifying and securing these non-negotiable foundations.
1. Secure boot and root of trust
The hardware root of trust is the most critical element in any embedded system.
Keys embedded in ROM or OTP at manufacturing cannot be updated once deployed.
If these keys rely on quantum-vulnerable algorithms, the device is permanently exposed.
2. Firmware signing and verification
Firmware integrity relies on digital signatures that must remain secure over the full device lifecycle.
Post-quantum algorithms introduce larger signatures and higher verification costs, impacting memory and boot design and must be anticipated early.
3. Device identity and key establishment
Provisioning, authentication, and secure communication rely on key exchange mechanisms that are directly impacted by quantum threats.
Post-quantum alternatives such as ML-KEM are required to ensure long-term confidentiality of device communications.
4. Systems with limited update capability
Many deployed devices cannot be upgraded to support post-quantum cryptography.This creates a structural risk requiring hardware redesign or system-level compensating controls.
SEALSQ post-quantum solutions

Quantum Shield - QS7001 security platform
QS7001 is a secure microcontroller platform designed to serve as a hardware root of trust for connected devices.
It enables:
- Secure key storage and device identity anchored in hardware
- Execution of cryptographic operations in a protected environment
- Integration of post-quantum cryptographic algorithms such as ML-KEM and ML-DSA
- Resistance to physical and side-channel attacks
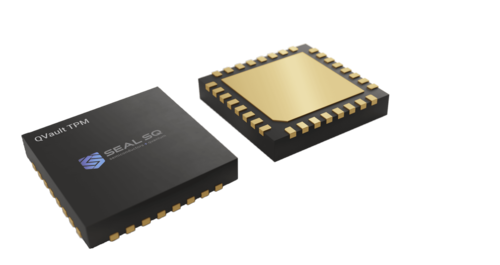
QVault TPM
QVault is a next-generation Trusted Platform Module designed to provide standardized, certifiable cryptographic services aligned with enterprise and industrial security requirements.

INeS PKI Platform
SEALSQ’s INeS PKI platform provides secure digital identity and certificate management capabilities designed for connected devices and regulated environments.
The platform supports:
- Device identity provisioning and lifecycle management
- Certificate issuance and management for embedded and IoT systems
- Integration with post-quantum and hybrid cryptographic approaches
- Secure onboarding and authentication of connected devices
Combined with SEALSQ hardware security platforms, INeS helps organizations strengthen trust infrastructures while preparing for evolving post-quantum security and compliance requirements.
Built for post-quantum transition
SEALSQ platforms are designed to support:
- Hybrid cryptography (classical + PQC)
- Progressive integration of post-quantum algorithms
- Long-term security across device lifecycles

Aligned with certification requirements
SEALSQ’s approach is structured around internationally recognized security standards:
- Common Criteria (EAL5+) for hardware assurance
- FIPS 140-3 for cryptographic module validation
- Trusted Computing Group (TCG) TPM standards
This combined model enables manufacturers to accelerate certification, reduce integration complexity, and prepare for evolving regulatory requirements.

.png)